The Ultimate Step-By-Step Guide to WordPress Security
You are here:
- Home
- Website Design And Development
- The Ultimate Step-By-Step Guide to WordPress Security

Hackers attack WordPress sites both big and small with over 90,978 attacks happening per minute. Fortunately, there are numerous ways you can protect your WordPress site.
Today, I want to share with you how you can make your WordPress site’s security air tight with basic through to advanced techniques. I’ll also explore how WordPress can be vulnerable to attacks, how hackers compromise websites, how to troubleshoot a hacked site and security plugins you can install.Is WordPress Secure?
With so many hackers attempting to infiltrate WordPress sites regularly, you may begin to wonder if WordPress is really secure at all. You can stop wondering because WordPress is inherently secure, though, there’s a caveat. The security team behind WordPress works diligently to neutralize any vulnerabilities that surface within the WordPress core. Security patches are included in core updates that are released consistently and on a regular basis. In fact, since WordPress was initially released, over 2,450 security vulnerabilities have been quickly patched. There are also times where fixes have been made in under 40 minutes of a vulnerability’s discovery The caveat is that you need to keep WordPress core up-to-date in order to apply all the security patches that are rolled out. Fortunately, updates can be pushed automatically or manually in a couple clicks. You can also choose to turn off automatic updates in case you want to run compatibility tests beforehand. This change is also covered later on in this post, but you can also check out Why You Should Have the Latest Version of WordPress, WordPress Core is Secure – Stop Telling People Otherwise and WordPress: It Ain’t Perfect – but Neither Are the People Who Use It for details. If you take away only one tip today, make it this one: keeping WordPress up-to-date is by far, the single most critical action you can do for the security of your site. Every other technique you apply is still necessary, but it’s not going to do you any good if the WordPress core itself is vulnerable and that happens if it’s not up-to-date. Fortunately, you can update your entire site in a few clicks from The Hub.Why Your Site is a Target
WordPress is secure, but the fact is, all websites are targets for hackers so no one is immune. Even a fresh install of WordPress with nothing on it, little to no traffic, and that’s kept up-to-date is still at risk. Overall, there are two main reasons why any site is hacked: money and hacktivism (defacing a site for political reasons such as to show support for a particular political party or influencing group). The American Economic Association reported that businesses and consumers lose $20 billion per year due to spam. According to a 2016 report by Sucuri, 100% of sites that were sampled were hacked in order to exploit them for profit, but four percent of them are simultaneously used for hacktivism. .Any and every site is a target no matter how teeny-tiny or gargantuan. The reason is that WordPress iteself is such a popular content management system (CMS) that it’s a natural target. Hackers can create a program, commonly referred to as bots or hackbots, that automatically and systematically scans for security holes and attacks hundreds of thousands of sites simultaneiously. The more sites that can be scanned and attacked, the greater the potential success rate for the hacker. WordPress as a target for hackers is similar to hitting a mansion-sized bull’s eye if you were playing paint ball. The chances of you being able to successfully splatter that target with paint over and over even from a great distance is almost certain. Since WordPress now powers 28% of all websites on the internet according to W3Techs, which is also the largest segment of websites using a known CMS, there are millions of sites that hackers can target. It’s all about the math, really. Smaller, less popular sites are a particularly great option for hackers because they’re less likely to be secure, since many owners of these sites may not know they’re actually a larger target than they realize. On the flip side, larger, more secure sites are still a target because there’s a greater audience available for hackers who want to inject and profit off spamif they can manage to get past the website’s defences. It’s important to recognize that while WordPress is secure when it’s kept up-to-date, no site is impervious to infiltration 100% of the time. For example, WordPress version 4.7.3 patched six XSS vulnerabilities in the REST API that could allow hackers to inject code into any WordPress site. It affected over 1.5 million sites according to Wordfence. Sucuri initially reported that roughly 67,000 WordPress sites were hacked and defaced by different hackers due to the discovered security hole. Once a patch was released, over one million sites weren’t immediately updated, whcih lead to them being hacked.How Hackers Compromise Websites
When writing code, it’s near impossible to not create any security holes whatsoever. When hackers find these vulnerabilities, they exploit them and you’re left with a compromised site. There are are also other ways a site could be vulnerable including human error such as using passwords that are easy to guess as well as insecure or unreliable hosting. There are a number of commonly exploited and potential WordPress vulnerabilities including: 1. SQL Injection (SQLI) – Occurs when SQL queries and statements can be entered and executed from a site’s URL 2. Cross-site Scripting (XSS) – A hacker can inject code into a site, typically through an input field 3. File Upload – A file with malicious code is uploaded to a server without restriction 4. Cross-Site Request Forgery (CSRF) – Code or strings are entered and executed from a site’s URL 5. Brute Force – Constantly trying to log in by guessing the admin’s account username and password 6. Denial of Service (DoS) – When a site goes down due to a steady stream of traffic coming from a hackbot 7. Distributed Denial of Service (DDoS) – Similar to a DoS attack, except the hackbot is sending traffic from multiple sources such as infected computers or routers 8. Open Redirect – Occurs due to a vulnerability and it’s a site’s page that’s redirected to a different one that’s set by a hacker and is often spam or a phishing site 9. Phishing (Identity Theft) – A site or page created by a hacker that looks like a well-known, commonly trusted site, but is used to collect login credentials by tricking a user to input their details 10. Malware – A malicious script or program with a purpose to infect a site or system 11. Local File Inclusion (LFI) – An attacker is able to control what file is executed at a scheduled time that was set up by the CMS or web app 12. Authentication Bypass – A security hole that enables a hacker to circumvent the login form and gain access to the site 13. Full Path Disclosure (FPD) – When the path to a site’s webroot is exposed such as when the directory listing, errors or warnings are visible 14. User Enumeration – Being able to determine a valid username to later use for brute force attacks by adding a string to the end of a WordPress site’s URL to request a user ID which may return an author’s profile with the valid username 15. XML External Entity (XXE) – An XML input that references an external entity and is processed poorly by improperly set up XML parser and can lead to confidential information disclosure 16. Security Bypass – Similar to authentication bypass, except that a hacker can circumvent the current security system that’s in place to gain access to some part of a site 17. Remote Code Execution (RCE) – A hacker has the ability to execute arbitrary code on a machine or site from a different machine or site 18. Remote File Inclusion (RFI) – Exploiting a reference to an external script on a site in order to exploit it to upload malware and all from an entirely different computer or site 19. Server Side Request Forgery (SSRF) – When a hacker can take control of a server either partially or totally to force it to execute requests remotely 20. Directory Traversal – Cases where HTTP can be exploited to access a site’s directories and execute commands outside of the server’s root directory While this isn’t a complete list of WordPress security vulnerabilities, they’re the most common ways a site is exploited, often through the use of a bot. Multiple vulnerabilities could also be exploited at the same time as well. According to Wordfence as well as a report by WP WhiteSecurity, XSS, SQLI and File upload vulnerabilities are the most commonly exploited security issues. Improperly coded plugins are also the largest culprit and accounts for 54% of these attacks, followed by the WordPress core and themes, respectively. It was also reported that 73% of WordPress sites are vulnerable to attack. For details, be sure to check out Category: Vulnerability, The Ultimate Guide to WordPress Spam, XML-RPC and Why It’s Time to Remove it for WordPress Security and A History of WordPress Security Exploits and What They Mean. With all the above in mind, this is why it’s important to take your WordPress site’s security seriously. Fortunately, there is a myriad of ways you can beef up your WordPress site’s security from straight forward tips to more complex steps that you can find below. I’ll start with the basics and get progressively more advanced as you work your way through this article.Basic, No-Nonsense Security Steps
It’s just as important that your computer’s secure as it is that your site is secure. Malware and viruses can infect your computer, which can spread to not only your WordPress site but hundreds of thousands of other WordPress sites. There are many ways you can ensure your computer stays as secure as possible. Here are basic tips to help you start stepping up the security of your computer and WordPress site: 1. Install a computer virus scanner to help prevent malware and viruses. Be sure the software can also clean up threats as well. 2. Schedule regular virus scans of your computer to be sure its not unknowingly infected. 3. Install a computer firewall or enable it if its included with your operating system or your virus scanner. 4. Don’t login to the admin dashboard or access your WordPress site when you have previously and are still logged in via a public WiFi or internet café since your credentials can be tracked or someone could be watching you enter in your login details. 5. Don’t log into WordPress through an unsecured internet connection or network. 6. Use a solid and trusted hosting provider who has an excellent reputation for security and reliability. 7. Only use strong passwords for your siteand force your users to use strong passwords as well by using a plugin such as Wordfence. 8. Don’t allow users to upload files to your site or carefully sonsider it beforehand since hackers could exploit the priviledge and upload malware. This also applies to uploading images such as avatars since sneaky snakes could name a malware file something similar to image-name.jpg.php and it may slip through the cracks. 9. Use File Transfer Protocol Secure (FTPS) instead of FTPwhich is unsecure to help prevent your connection from being controlled or monitored. 10. Alternatively, you can use SSH File Transfer Protocol (SFTP) instead of FTP because the former is also more secure. 11. Only give admin access to those you know and trust. 12. Similarly, only assign the editor user role to people you know and trust. 13. Install a security plugin such as Defenderand use the free version at the very least. 14. Enable audit logging in Defender to monitor and track the activityof editors, authors, other admins, users and hackers you’re concerned about, especially if you suspect they could be distributing malware. 15. Only allow trusted people have access to your hosting account or better yet, don’t give anyone access to it unless it’s absolutely necessary. If it is, create an account for them with limited access to only what they need to access and nothing more. 16. Don’t give out FTP credentials or create FTP accounts for people you don’t trust or know well. 17. If you’re not currently using FTPS/FTP, delete any active accounts or disable the feature until the next time you need it to prevent your connection and credentials from being stolen. 18. Backup your site (or network!) oftenand also schedule backups to prevent a lapse in archives that are available in case you need to restore your site. 19. Test your most current backupsto ensure they work and include everything that was meant to be backed up. 20. Backup your backupsto ensure you’re not going to be left in the lurch in case a backup doesn’t work as expected. 21. Keep WordPress up-to-dateat all times. 22. Similarly, you should also keep your plugins, themes and scripts up-to-date at all times as well. 23. Review the code of any plugin, theme or script you’re using to make sure it’s coded well. Pay attention to its reviews and look for any lingering security issues that have not been resolved. 24. Keep up to date with WordPress newsletterssuch as the WhiP to ensure you’re up-to-date on the latest WordPress and related security issues. 26. Don’t use plugins, themes or scripts with known security issues. Remove them immediately and notify the developer. 27. Test plugins, themes and sripts in a local staging environment before installing and activating them on a live site. 28. Use a content delivery network (CDN)to help prevent DoS and DDoS attacks. 29. Install and force the use of an SSL certificatefor your Multisite network or for your single install of WordPress. Remember this is just the beginning so be sure to work your way through this article and apply as many of these security steps as you can for a more reliable security strategy. You can also use the .htaccess to NGINX Converter to take the examples below and automatically generate code you can use for NGINX servers.Security Through Obscurity
If you were to ask, many WordPress developers would chant, “Security through obscurity is no security” or some form of that. They’re not wrong, but it also wouldn’t hurt to use it and it some cases, it may help. Security through obscurity means hiding an aspect of a software or web application in an attempt to secure it with the hopes that if a hacker can’t find what you’re hiding, it remains safe. In the case of WordPress, this means hiding parts of your site such as the login page, for example, hoping that a hacker couldn’t find it. This isn’t a reliable security tactic because most hackers are experienced enough that they could easily find a way around the obscurity tactic to infiltrate your site. However, WP WhiteSecurity previously reported that only 8% of sites are manually hacked by brute force attacks. Most sites are infiltrated automatically and systematically by bots. Since bots are set up to attack a site with a typical setup and move on if the hack isn’t immediately successful, there’s a chance (albeit a small one) that security through obscurity can work a small percentage of the time. This is especially true if the hacker is inexperienced. These kinds of tactics are also a part of the recommended security hardening steps in the WordPress Codex. That being said, it’s true that you shouldn’t rely solely on security through obscurity to protect your WordPress site because it isn’t going to work at least most of the time. It’s far, far away from being a solid security strategy. It can still help in a small number of cases as previously mentioned so you can still use this method, but if you do, you must also use a well-rounded set of security strategies that span far outside of obscurity tactics. For details, check out Changing Your WordPress Database Prefix to Improve Security. With all that in mind, here is the most common security through obscurity tactics that you can choose to either bypass or use as a part of your overall security strategy.Obscurity Through the wp-config.php File
There are a few common edits you can make to your wp-config.php file that are considered to be security through obscruity tactics and you can find them below. For more details on the wp-config.php file and editing it, check out The WordPress wp-config File: A Comprehensive Guide and How to Tweak wp-config.php to Protect Your WordPress Site. The changes below can also be made without tweaking code if you use Defender.Disabling the Plugin and Theme Editor
In the admin dashboard, there’s an editor where you can adjust and save the code of the files for the plugins and themes you have installed. You can access the theme editor by going to Appearance > Editor. Similarly, the plugin editor can be found under Plugins > Editor.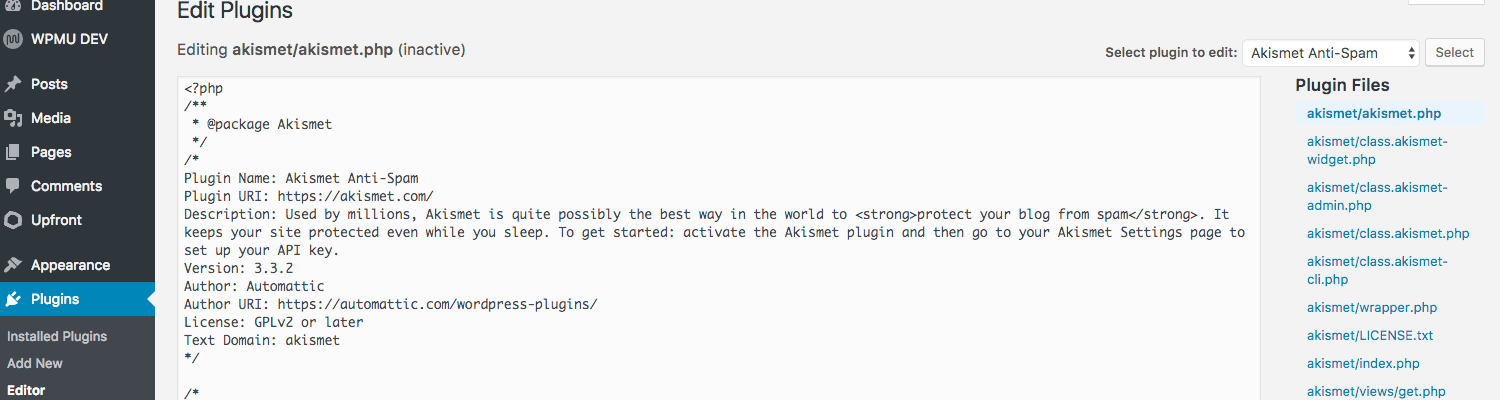 It’s considered a security risk by many developers because a hacker who has access to your admin dashboard could edit theme and plugin files directly without needing to hack their way further into your site’s directories.
Other developers would argue that if a hacker already has access to your admin dashboard, it’s already game over.
At the same time, why make it easier for hackers to completely compromise your site when there would otherwise be a chance that you could stop it in its tracks before it gets worse? You may as well make it a bit more difficult for hackers to buy you some time to remedy the situation in the meantime.
You can add this code to your wp-config.php file to disable the theme and plugin editors:
It’s considered a security risk by many developers because a hacker who has access to your admin dashboard could edit theme and plugin files directly without needing to hack their way further into your site’s directories.
Other developers would argue that if a hacker already has access to your admin dashboard, it’s already game over.
At the same time, why make it easier for hackers to completely compromise your site when there would otherwise be a chance that you could stop it in its tracks before it gets worse? You may as well make it a bit more difficult for hackers to buy you some time to remedy the situation in the meantime.
You can add this code to your wp-config.php file to disable the theme and plugin editors:
Relocate the wp-config.php File
Your site’s wp-config.php file includes a lot of important and sensitive information that needs to be kept private. Moving it away from its default location can make it more difficult for hackers to anticipate where it’s going to be when they try to weasel their way into that file. If your WordPress site is located in the root instead of a sub-directory, you can safely move your wp-config.php file one directory up as long as there isn’t already a file there with the same name. You can also move your wp-config.php anywhere you want as long as you create a new file with the same name and with the code below in its original location: Don’t forget to change /path/to/wp-config.php to the actual path of your wp-config.php file, where ever you moved it.Change the Database Prefix
By default, tables in your WordPress database have a wp_ prefix. I know, original, right? You can leave it as is, but it’s one less item hackers need to guess in order to hack into your site so changing this to something random and complex can be helpful.Add Rules to your .htaccess File
There are also some obscruity tactics you can set up by adding rules to your .htaccess file and you can find them below.Protecting Important Files
You can deny access to critical files including .htaccess, wp-config.php, php.ini and your error logs by adding the rules below from the WordPress Codex: If you have a php5.ini or php7.ini file instead of php.ini, you can replace php.ini on line one with the actual name of the file.Restricting Access to PHP Files
In addition to the above, you should also limit access to your PHP files, since hackers could inject malware into them. You can restrict access to WordPress PHP files by adding the following rules from Acunetix to your .htaccess file:Securing the /wp-includes/ Directory
The /wp-includes/ also have many critical files that could be exploited if you don’t otherwise protect them. The rules below from WP Explorer should do the trick and restrict access to this directory:Restricting Access to the Admin Dashboard
When a hacker accesses the WordPress login page and tries to guess the username and password for the administrator account, it’s called a brute force attack. Limiting the users that are allowed to see the log in page and access the admin dashboard can reduce some of those attacks. While it’s possible for them to access the login form via bots and without actually needing to visit the page, you should still see a significant reduction in brute force attacks in most cases by restricting access to these admin pages. You can restrict access to your admin dashboard to a few static IP addresses by adding the following to to your .htaccess file: Lines one and two redirect users to a 404 error page if they try to visit the admin dashboard from a different IP address than what’s defined in this rule. It helps resolve possible redirect loops so your site doesn’t appear to be down. Just be sure to replace /path-to-your-site/ with the actual path of your WordPress site. Also be sure to replace IP Address One, IP Address Two and IP Address Three with three real IP addresses that you want to authorize so users from those locations can access the admin area. Keep in mind that if you plan to travel, you should update or remove this rule before you go, otherwise you would get locked out of your site. If you only want to include one IP address, you can remove lines nine and 10. Alternatively, you can add line 10 as many times as you want. Don’t forget to replace IP Address Three for each line you add. If you have a dynamic IP address, or you have users that need to login, you can add this rule instead: Similar to the previous rule, be sure to replace /path-to-your-site/ with the correct path to your site. Also, replace your-site.com with your actual domain.Preventing Directory Browsing
By default, it’s possible for a user (read: hacker) to access important folders in your site by including the full path to those directories in the address bar of their browser. For example, they could see all the content in your uploads folder if they entered your-site.com/wp-content/uploads/. While it wouldn’t be possible for them to edit any of those files if you have properly set your file permissions, knowing where your files are located makes it that much easier for them to attack since they already know where everything is located. Fortunately, you can add this rule to your .htaccess file to prevent directory browsing:Prevent Username Enumeration
Username Enumeration occurs when a hacker is able to tag on a string at the end of a WordPress site’s URL that requests a user ID. If that user also has an author user role and has published content on the site, the URL would return that author’s page along with the account’s username. At this point, the hacker would know a valid username and half their work is done. They would only need to guess the password for this account in order to access it. Preventing username enumeration can make it that much more difficult for hackers to successfully hack your site. Include the below from Acunetix in your .htaccess file to prevent username enumeration:Delete Unneeded Files
There are a few files that aren’t needed any longer once WordPress has been successfully installed. Deleting them prevents sensitive information from accidentally being added to them, which could give hackers a potential entry point into your site. You can safely delete these files:- html
- /wp-admin/install.php
- wp-config-sample.php
Changing Your File and Directory Structure
Speaking of the WordPress records that are publicly available as an opensource platform, there’s a lot more a hacker could easily look up and use to compromise your site. For example, they can look up the default WordPress file and directory structure to pinpoint exactly where they want to strike your site. You can change up your site’s structure and relocate your files and directories in whatever way you want. For details, check out How to Change Your WordPress File and Directory Structure.Change Your Default Username
When you install WordPress, the default username that’s included during the setup process is “admin.” While you could leave the name as is, it’s one less thing that a hacker needs to know to infiltrate your site through brute force. If you try logging into WordPress, but you enter the wrong password for a correct username, a message is returned and lets you know this fact. This means a hacker can tell if they have correctly guessed a username. Since “admin” is commonly used as a username, it’s an obvious place for a hacker to start when they’re attacking your site by brute force. If you still use that account name, the hacker would be able to tell based on the WordPress message they see and they can keep trying to guess your password until they get it right. Changing your username from the default option makes it more difficult for hackers to successfully attack your site via brute force. For details on making this change, check out How to Change Your WordPress Admin Username.Hide the WordPress Login Page
While we’re on the subject of the WordPress login page and brute force attacks, you could hide your login page altogether. That way, hackers would have a heck of a time even attempting a brute force attack. While it’s possible to circumvent the need to visit the login page to attempt brute force attacks through the use of a hackbot, it can still significantly reduce the amount of brute force attacks your site experiences. To hide your login page, check out Limit Access to the WordPress Login Page to Specific IP Addresses, Hiding Your WordPress Login Page from Hackers with Code and How to Hide Your WordPress Login Page From Hackers and Brute Force.Remove the WordPress Version Number
As previously mentioned above, it’s helpful to your site’s security to prevent hackers from being able to discover what version of WordPress you’re using. Besides deleting the readme.html file as suggested above, you can also remove any mention of the WordPress version throughout your entire site. For details, check out How to Hide Your WordPress Version Number.WordPress Security Best Practices
Securing WordPress is all about patching up as many vulnerabilities as possible since that’s a hacker’s ticket into your site. They’re looking for the quickest entry way to hack a site rather than a long winded battle. WordPress sites with security holes are targeted for that reason. That means you can effectively block 99.99% of attacks on your website by addressing these security issues. Here are WordPress security techniques and best practices to help secure your WordPress site.Use a Security Plugin
Many or most of the security techniques mentioned here can be applied quickly with a security plugin. Installing one and keeping it active is a simple and excellent way to ensure your site is protected and without having to remember to apply all the security tactics yourself. WordPress itself is secure as long as you keep it updated, but new vulnerabilities surface as hackers find them. A security plugin helps protect you while the WordPress security team works on a fix to release in the next core update. You can find a list of reliable and solid security plugins later on, but remember to install one if you don’t have one on your site already.Run Regular Scans
Once you have installed and activated a security plugin, it’s important to set up regular scans. Most of them have this option and it’s crucial to enable it. Without regular security scans, a vulnerability could go undetected and it could potentially lead to your site being compromised without you even knowing about it.Review Your Access Logs Often
When you set up your site with your host, logs were also initiated at the same time. Somewhere in your account, you should have error and access logs being stored. The exact location of them is dependent on your hosting provider. You should check with them if you’re not sure where to find them. Your access logs are a record of each time someone accessed your site and more importantly when critical files were accessed or there was an attempt to visit them. If you monitor these logs regularly, you can keep an eye on any unusual activity. For example, when there were attempts to access files that regular visitors would try to view such as the .htaccess or wp-config.php files. You would also be able to see when these files were successfully accessed, which would indicate that your site was hacked. If you can stay on top of these logs and look over them regularly, you can be in the know if there are threats that need to be squashed right away. Reviewing your access logs manually is incredibly timeconsuming and tedious so it’s a lot more efficient to install a security plugin such as Defender that consolidates these logs for you and notifies you if there was a breach in security or close to it.Use the Correct File Permissions
Many WordPress core files as well as plugin, theme, script and custom or uploaded files contain critical and sensitive details. It’s important to ensure only authorized parties are able to access them. Setting the correct file permissions ensures that this happens. You can check out Understanding File Permissions and Using Them to Secure Your Site for details.Disable XML-RPC
XML-RPC is an API that WordPress uses for its trackback and pingback features as well for the Jetpack plugin. While this API is useful if you use any of these, it can also be exploited by hackers as a means for brute force attacks. Even if you have a strong password, brute force attacks use up a lot of your server’s resources. If your hosting plan isn’t sufficient, your site could go down after all your server’s resources are used up. To prevent hackers from exploiting this API, you can disable XML-RPC on your site.Prevent Spam
Spam in WordPress is a lot more than just annoying. It can lead to brute force and DDoS attacks as well as XSS vulnerabilities. Preventing spam from ever crossing your site is an important part of keeping WordPress secure. There are many ways you can protect yourself from spam including the use of plugins.Use Two-Factor Authentication
Requiring logging in to be approved by a second step such as accepting the request through a notification on your smartphone, for example, is called two-factor authentication. Using a plugin to enable this feature helps further protect you from brute force attacks in case a hacker is able to guess your password. Additional Edits to the wp-config.php File Including the security techniques mentioned earlier, there are also other additions you can make to your wp-config.php file. For details on any of these edits.Change Your Security Keys
The wp-config.php file includes security keys that help encrypt information stored in cookies. Changing them every now and again effectively logs out all users, including hackers in many cases where they hijack a browser connection, for example. You can change your security keys by going to the WordPress Security Key Generator and copy and pasting what’s on that page, then replacing the existing keys in your wp-config.php file. The existing security keys should look similar to the example below: You can also replace your security keys in a couple clicks using Defender.Force SSL
Once you have an SSL certificate installed for your domain, you should force its use so anyone who visits your site immediately accesses it with the SSL certificate since it ensures a secure connection. Add the following to your wp-config.php file before the “happy blogging” line: There’s one final step. You also need to add the line below to your .htacessfile: Be sure to replace www.mysite.com with your real domain.Force the Use of FTPS
Additionally, you can force users to use FTPS over the insecure FTP automatically by adding the line below above the “happy blogging” part:Enforcing SFTP
Similarly, you can force the use of SFTP if your host has it enabled to ensure your connection is secure when you use SSH and the command line. To enforce the use of SFTP, add the following above – you guessed it! – the “happy blogging” line:Turn off WP_DEBUG
Unless you’re encountering errors on your site, you should disable front-end error reporting. You can do this by turning of WP_DEBUG by editing the following line in your wp-config.php file: Change true to false, then save the file and you’re all set. Alternatively, you can leave WP_DEBUG on, but enable private logging of errors by leaving the line above as-is, then following it with this:Auto-Update the WordPress Core
This tactic isn’t for anyone who wants to thoroughly test updates before applying them, but if you don’t mind updates being automatically applied, you can do that by editing this similar line in the wp-config.php file to appear like this:Further Editing the .htaccess File
There are also additional and recommended edits you can make to your .htaccess file to improve your WordPress site’s security. For details on any of these changes, check out A Comprehensive Guide to Editing .htaccess for WordPress Security.Restrict PHP File Execution
In the event that your site is hacked, you can still prevent hackers from being able to execute the malware they upload to your site by adding the rule below to your .htaccess file: It restricts PHP files from being executed from the uploads folder since that’s an incredibly common place for hackers to upload malware.Protecting Your Site Against Script Injections
You’re on a serious roll now so you may as well prevent hackers from being able to inject malware into your PHP files by adding the following to your .htaccess file:Limit Login Attempts
By default, WordPress doesn’t limit the number of times you can attempt to log in or retreive your password. This gives hackers near infinite leway to continue with their brute force attacks until they’re successful. Instead of letting that happen, you can install a security plugin that lets you limit the number of login attempts. You can peruse the list that can be found further down to find a suitable plugin. For example, you can limit the number of login attempts that are allowed without touching any code by using Defender. It can be set up in a couple clicks as well.Install a Server Firewall
Installing a firewall on your server is an excellent way to prevent hackers from being able to access your site and server right from the get go. This isn’t to be confused with a web application firewall (WAF) such as the one found in the Wordfence plugin. In the case of WordPress, a WAF is positioned inside your site instead of outside where it’s actually useful. The reasoning behind this is similar to the obscurity tactics mentioned earlier. If a hacker has already infiltrated your site, they’re in and a firewall inside your site isn’t going to stop them. The only way a hacker can be sufficiently stopped in their tracks is if you install a firewall on your server such as with the free ConfigServer Security & Firewall. Keep in mind that your host may already have a server-level firewall already installed for you. If you’re not sure, it’s best to contact them and ask. Still, a WAF or a server-level firewall as well is better than using no firewall at all.WordPress Security with Plugins
For continued protection and security of your WordPress site’s it best to use a plugin. Below are the top security plugins that are reliable, updated often and are top-quality. You don’t need to install all of them. You can install one or install two with complementing features. Just be sure not to enable the same features in both plugins to prevent compatibility issues.Conclusion
By now, you’re all set and your WordPress site is safe and secure. While this isn’t absolutely everything you need to know about WordPress security (it would be difficult to add everything into one article!), it’s an exhaustive list of solid techniques to secure your site. As Publishes On wpmudevRecent Posts
Contact Us